Spyware is the key!, New evidence! The mysterious hacker identity of the cyber attack on Western Polytechnic University has been locked down
Recently, the National Computer Virus Emergency Response Center and 360 Company conducted a technical analysis of a spyware called "Second Date", and the analysis report showed that the software is a network spy weapon developed by the National Security Agency of the United States. It is reported that during the collaboration between the National Computer Virus Emergency Response Center and 360 Company in investigating the cyber attack on Northwestern Polytechnical University by the US National Security Agency, multiple samples of this spyware were successfully extracted, and the true identities of the US National Security Agency staff behind this cyber espionage operation were identified.
According to a technical analysis report, "Second Date" spyware is a network spy weapon developed by the US National Security Agency. The software can achieve malicious functions such as network traffic eavesdropping and hijacking, man in the middle attack, and inserting malicious code. When combined with other malicious software, it can complete complex network "spying" activities.
Du Zhenhua, Senior Engineer of the National Computer Virus Emergency Response Center: This software is a high-tech network espionage tool that allows attackers to fully take over the attacked network devices and the network traffic flowing through these network devices, thereby achieving long-term theft of hosts and users in the target network. At the same time, it can also serve as a "forward base" for the next stage of attacks, delivering more network attack weapons to the target network at any time.
According to experts, "second date" spyware has long resided on network boundary devices such as gateways, boundary routers, and firewalls. Its main functions include network traffic sniffing, network session tracking, traffic redirection hijacking, and traffic tampering. In addition, the "Second Date" spyware supports running on various operating systems and is compatible with multiple architectures, making it widely applicable.
Du Zhenhua, Senior Engineer of the National Computer Virus Emergency Response Center: This spyware is usually used in conjunction with various network device vulnerability attack tools targeting firewalls and network routers in specific intrusion action offices. Once the vulnerability attack is successful and the attacker successfully obtains control permissions of the target network device, they can implant this network spyware into the target network device.
The report shows that the National Computer Virus Emergency Response Center and 360 Company, together with their partners in the industry, have carried out technical investigations around the world. After tracing the source layer by layer, they found that thousands of network devices all over the world are still secretly running "second date" spyware and its derivatives, and found springboard servers remotely controlled by the National Security Agency of the United States, most of which are distributed in Germany, Japan, South Korea, India and Taiwan, China, China.
Du Zhenhua, Senior Engineer of the National Computer Virus Emergency Response Center: With the joint cooperation of industry partners from multiple countries, our joint investigation work has made breakthrough progress. At present, the real identities of the National Security Agency personnel who launched a cyber attack against Northwestern Polytechnical University have been successfully identified.
Analysis Report on Spyware for "Second Date": Network Attack: The Real Identity of American Personnel Related to Northwestern Polytechnical University Locked
Recently, the National Computer Virus Emergency Response Center and 360 Company conducted a technical analysis on a "spy" software called "Second Date". This "spy" software targets gateway device platforms such as routers based on FreeBSD, Linux, Sun Solar, Juniper JunOS, etc. It can achieve malicious functions such as network traffic eavesdropping and hijacking, man in the middle attack, and inserting malicious code, thereby cooperating with other "spy" software to complete complex network "spy" activities.
According to internal NSA documents leaked by the Shadow Brokers, the malware is a network "spy" weapon developed by the US National Security Agency. "SecondDate" spyware is a specialized tool for man in the middle attacks, typically residing on boundary devices of the target network, sniffing network traffic and hijacking or tampering with specific network sessions as needed.
During the collaboration between the National Computer Virus Emergency Response Center and 360 Company in investigating the cyber attack on Northwestern Polytechnical University by the US National Security Agency, multiple samples of this spyware were successfully extracted, and the true identities of the US National Security Agency staff behind this cyber espionage operation were identified.
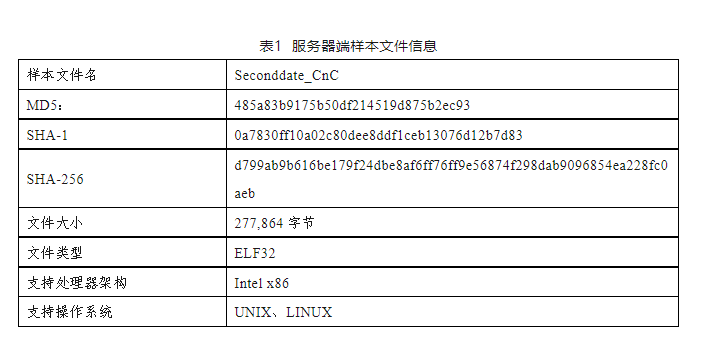
1、 Basic information
The "Second Date" spyware is mainly deployed on target network boundary devices, secretly monitoring network traffic, and accurately selecting specific network sessions for redirection, hijacking, and tampering as needed.
Technical analysis has found that "SecondDate" spyware is a high-tech network spying tool. Developers should have a strong foundation in network technology, especially in network firewall technology, which is almost equivalent to installing a set of content filtering firewalls and proxy servers on the target network device, allowing attackers to fully take over the target network device and the network traffic flowing through it, thereby achieving long-term theft of other hosts and users in the target network, and serving as a "forward base" for attacks, ready to deliver more network attack weapons to the target network at any time.
2、 Specific functions
The "Second Date" spyware stays on network boundary devices such as gateways, boundary routers, and firewalls for a long time, and can accurately filter and automatically hijack massive data traffic, achieving man in the middle attack function. Its main functions include network traffic sniffing, network session tracking, traffic redirection hijacking, traffic tampering, etc.
3、 Technical analysis
This "spyware" software targets network device platforms such as routers and firewalls. SecondDate supports distributed deployment and consists of server-side and client-side programs. Attackers implant client-side programs into target network devices through other means in advance, and then use server-side programs to command and control the client. The main workflow and technical analysis results are as follows:
Server side
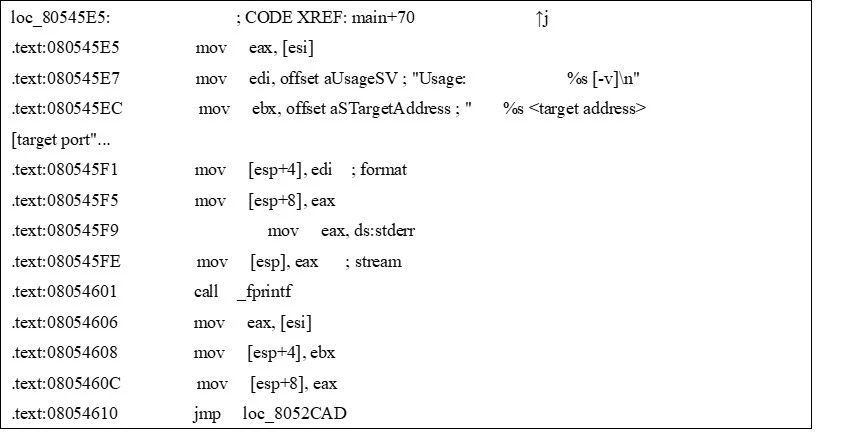
The main function of the server-side is to establish a connection with the client and issue control rules, allowing the client to perform corresponding malicious operations. As shown in Table 1, Figure 1, Figure 2, and Figure 3.
1. Connecting clients
Establish a connection with the client by specifying the client IP and port number in the command line parameters.
Figure 1 Establishing a connection with the client
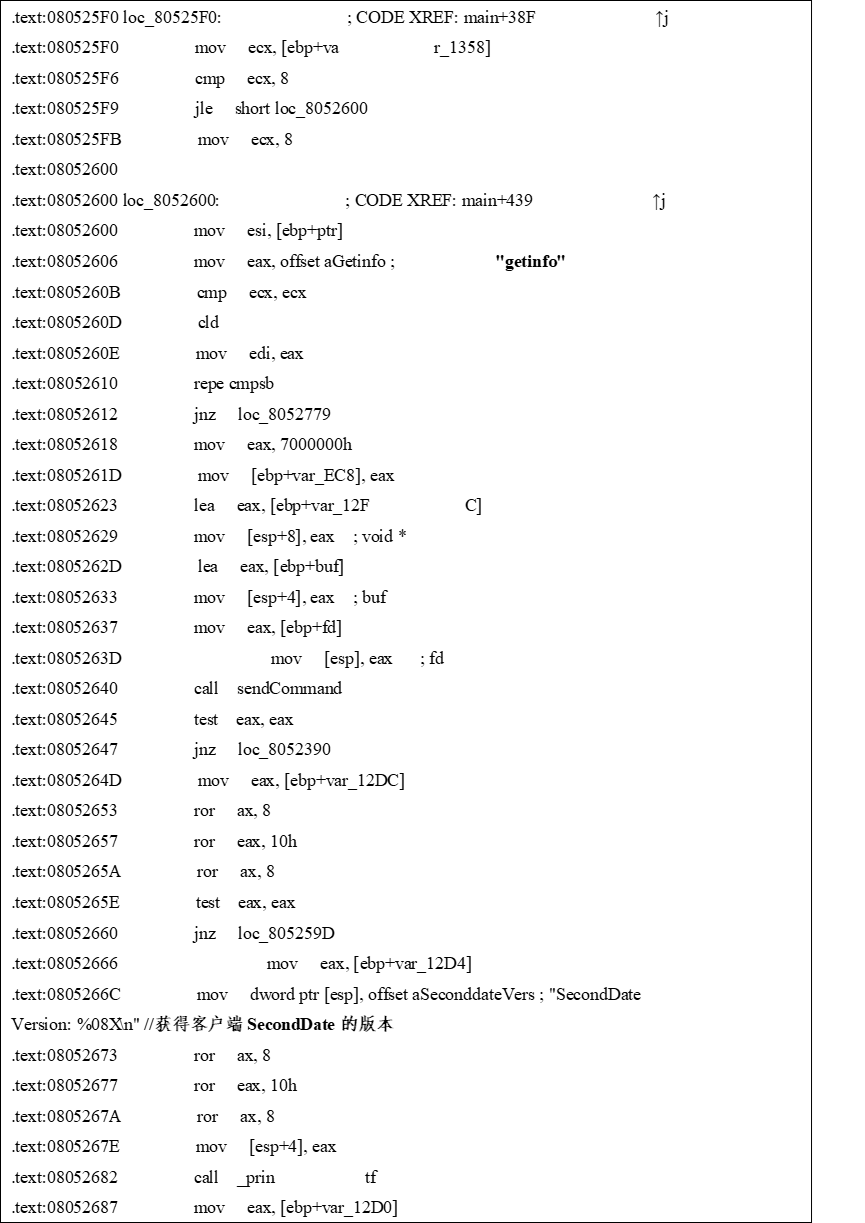
2. Obtain the current status of the client
Figure 2 Obtaining Client Status Information
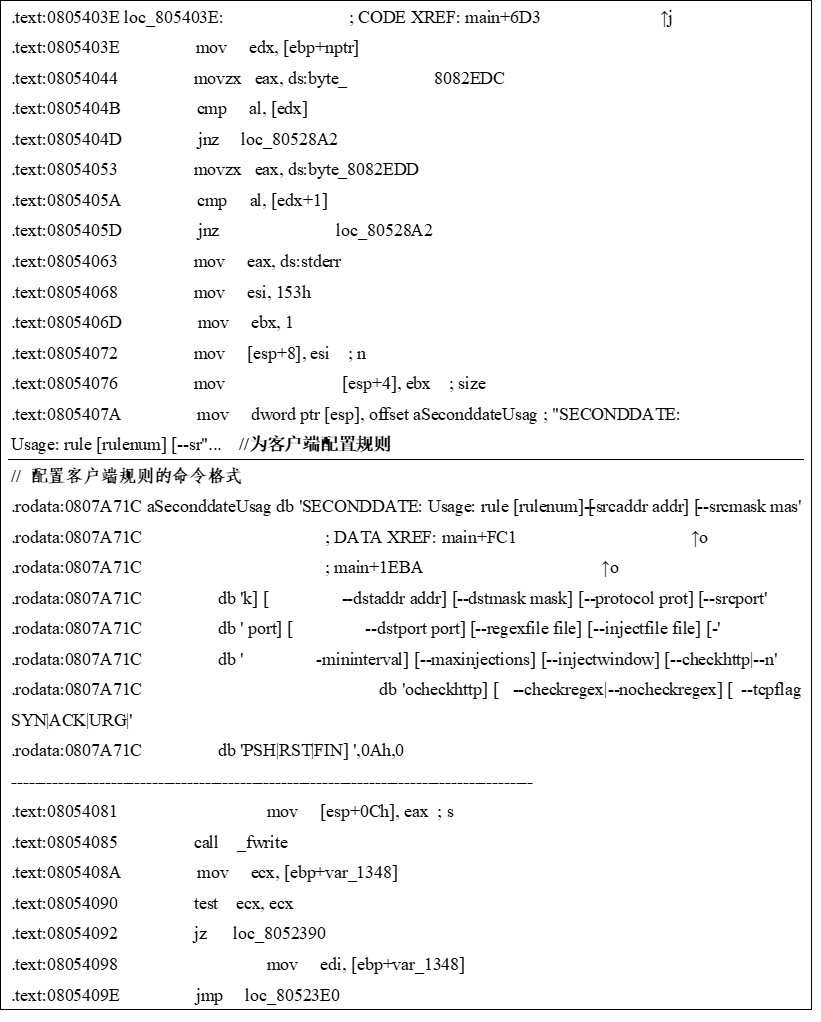
3. Configure client rules
Figure 3: Configure Client Rules
As shown in Figure 3, attackers can filter network traffic by specifying source IP address, source port, destination IP address, destination port, protocol type, TCP flag, etc. They can also specify matching regular expression files to obtain traffic with specific content, and can insert files containing specific content into the traffic.
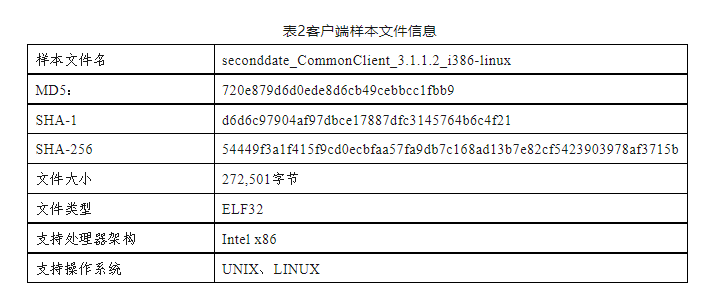
client
From the analysis results, it can be seen that after the client is implanted and configured with corresponding rules, it can run silently in the background of network devices. Attackers can use the server side for control or directly log in to the background of network devices for command control. As shown in Table 2, Figure 4, Figure 5, and Figure 6.
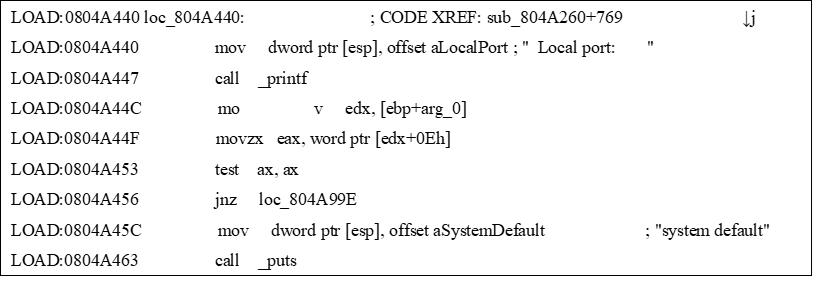
1. Specify local port
Figure 4: Client specified local port
2. Execute corresponding operations according to instruction rules
Figure 5: Client Execution Control Instructions
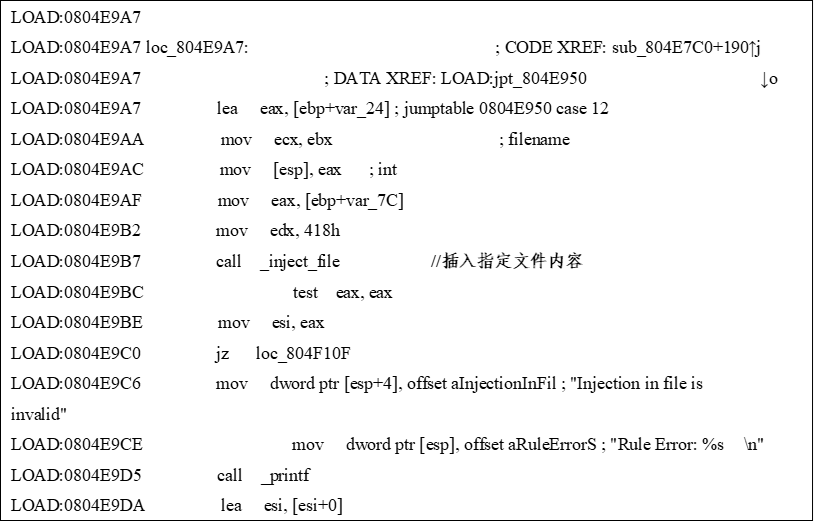
3. Insert file
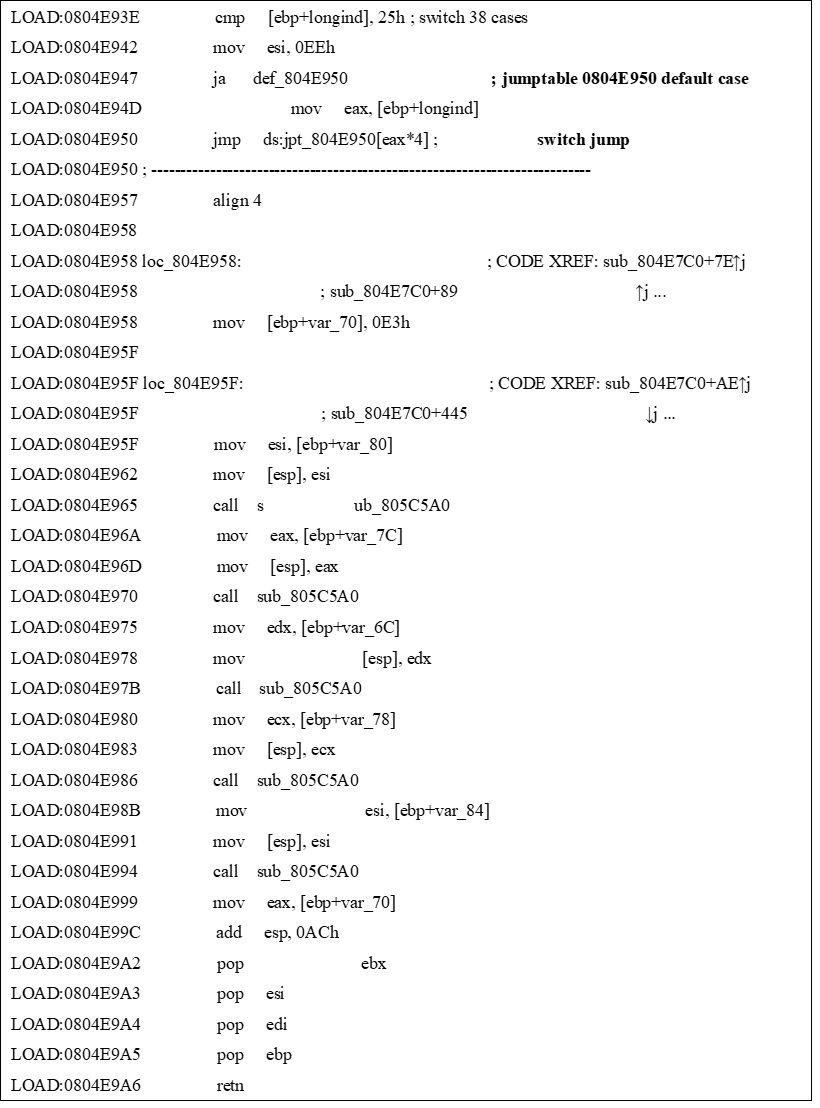
Figure 6 Client Execution File Insertion Instruction
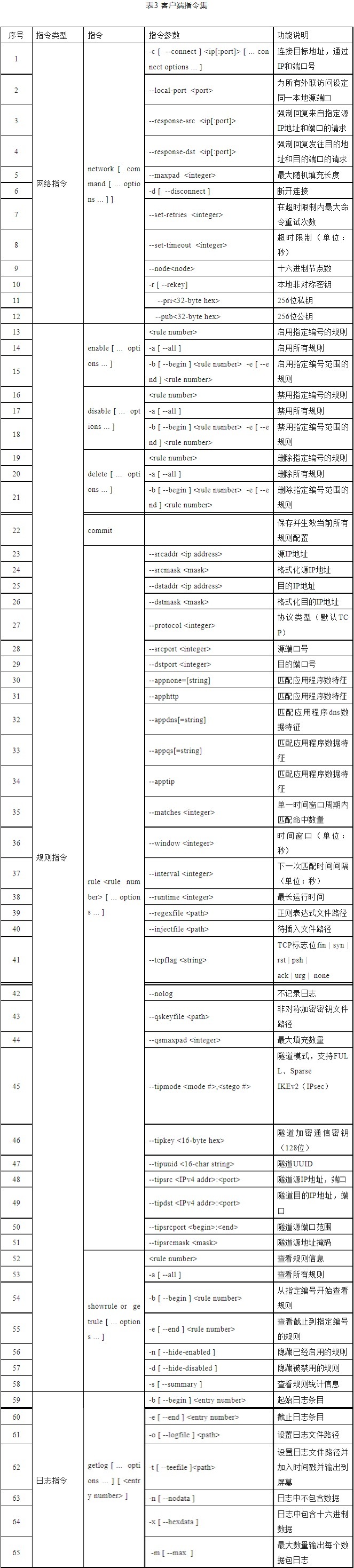
4. Instruction set
After analysis, the main instructions supported by the client and their functional descriptions are shown in Table 3.
The client instruction set is very rich and can achieve malicious operations such as content filtering of network traffic, man in the middle hijacking, and content injection.
4、 Usage environment
The "Second Date" spyware supports running on various operating systems such as Linux, FreeBSD, Solaris, JunOS, and is compatible with multiple architectures such as i386, x86, x64, SPARC, and has a wide range of applications.
5、 Implantation method
"Second date" spyware is usually used in conjunction with various network device vulnerability attack tools targeting firewalls and routers in specific intrusion action offices. After successful vulnerability attacks and obtaining corresponding permissions, it is implanted into the target device.
6、 Using control methods
The "Second Date" spyware is divided into a server and a control end. The server is deployed on target network boundary devices and monitors and filters all traffic in real-time through underlying drivers; After the control end triggers the activation mechanism by sending specially constructed data packets, the server parses the reconnection IP address from the activation packet and actively reconnects. The network connection uses UDP protocol, with encrypted communication throughout the entire process and random communication ports. The control end can remotely configure the working mode and hijacking targets of the server, and select any target within the network to carry out man in the middle attacks according to actual needs.
We carried out technical investigations with our industry partners around the world. After tracing the source layer by layer, we found that thousands of network devices all over the world are still secretly running "second date" spyware and its derivatives, and found that springboard servers remotely controlled by the National Security Administration of the United States, most of which are distributed in Germany, Japan, South Korea, India and Taiwan, China, China. With the joint efforts of industry partners from multiple countries, we have made significant breakthroughs in our work and have successfully identified the true identities of the National Security Agency personnel who launched a cyber attack on Northwestern Polytechnical University.
With the continuous enhancement of China's comprehensive national strength and profound changes in the international strategic landscape, overseas "spy" intelligence agencies are increasing their efforts to carry out espionage and intelligence activities in China. Carrying out "spy" and secret theft activities through the internet has become one of the main means.
In this context, the Chinese government, industry leading enterprises, universities, medical institutions, research institutions, etc. should accelerate the investigation of their own network "spy" attack clues and security risks, cooperate with capable network security companies to obtain digital security services, rely on big data, platforms, probes, experts to build security operation centers, and obtain digital security capabilities at low cost and high efficiency. Realize the ability to "see" all network assets, network situations, and national level espionage attacks, with core security capabilities such as "handling" security risks, advanced threats, and espionage operations. Ultimately, it can analyze, discover, block, clean, and recover in real time.