Poisoning corporate marketing accounts? First nationwide! Police: Do not open such documents. Personnel | enterprises | poisoning
Poison the enterprise marketing account! Have you heard of it?
It is to first launch Trojan programs to gain the trust of enterprise sales personnel, and then redirect customers within the enterprise's marketing account to overseas wire fraud groups to carry out fraud. Take a look at the case.
Case Review
In April 2023, the Cybersecurity Bureau of Hangzhou Public Security Bureau in Zhejiang Province discovered during work that multiple criminal gangs were using Trojan horse control programs to commit infringement on enterprises on online platforms.
After investigation by the police, it was found that the criminal gang obtained control over the company's marketing account through targeted online Trojan programs and offline shopping malls to gain the trust of sales personnel.

Finally, they will impersonate the identity of employees of the victim company and attract their customers to overseas wire fraud groups through "attracting large groups and sending red envelopes", providing them with "gold powder" and implementing precise fraud.
Technique Analysis
There are two ways to poison, one is to target online Trojan programs:
Zhang from Hubei is usually idle. In March of this year, he saw on foreign social media that someone was publicly recruiting personnel to launch Trojan viruses. The threshold is low and the salary is considerable.
As long as you contact the staff on the company's official website, pretend to talk about business, and send files containing Trojan viruses, it is considered to be half done. If the enterprise staff opens this file, the Trojan virus can invade the enterprise, and Zhang can receive commissions.

Without hesitation, Zhang started working and unexpectedly earned 100000 yuan in just one week. He immediately told his family and friends about this way of making money, so three or four people formed a small team to specialize in this matter.
Another way is to wait for an opportunity in offline shopping malls to log in to the enterprise marketing account:
Zhang is from Linquan County, Anhui Province, and is one of the local promoters of the gang. He is 27 years old this year. He himself is an unemployed wanderer who has been wandering around internet cafes and other places for years.
Last March, he signed up to participate in the "buying and selling" of this gang and formed a four person team to operate in pairs. One person is responsible for sales, while the other person takes advantage of the teller's distraction and scans the QR code with his phone to log in to the employee's corporate marketing account in the background.
As long as this step is achieved, their work is considered complete.
Over the course of several months, their four member small group ran through major shopping malls across the country, first from Jiangsu to Zhejiang, and then to Guangdong, Chongqing, Shaanxi, and Hubei.
The salary has also increased from 800 yuan/account, 1000 yuan/account, to 10000 yuan per day without any account assessment. At its peak, they earned 800000 yuan per month.
While they were still dreaming of making big money, they didn't expect to be targeted by the police.
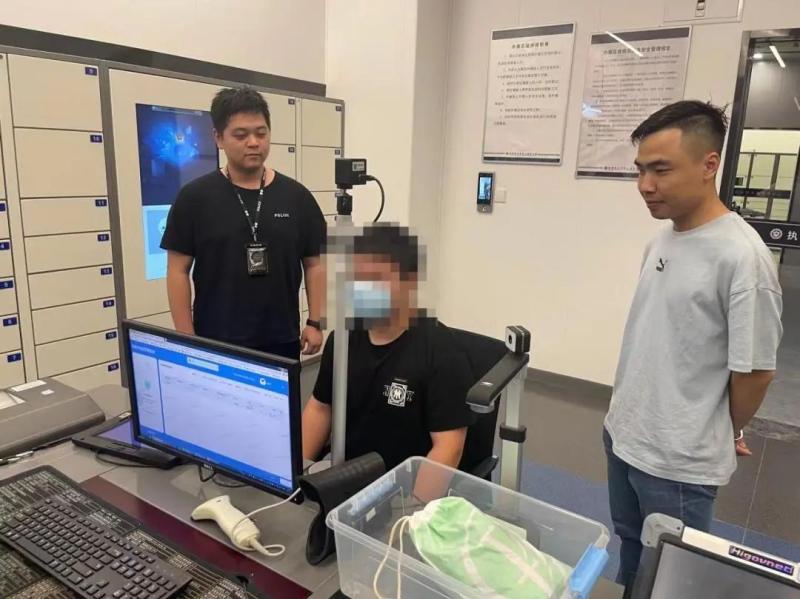
Arrest and capture
After finding out the criminal methods and chains of the gang, recently, under the guidance of the Ministry of Cyber Security and the Provincial Department of Cyber Security Corps, the Cyber Police Sub bureau, together with the Xiaoshan, Linping, Qiantang and Shangcheng Sub bureaus, went to Hunan, Hebei, Henan, Guangdong and Anhui provinces to carry out centralized network collection operations, and captured a total of 39 suspect from 7 gangs, 35 of whom were taken compulsory criminal detention measures according to law for suspected of illegally controlling the computer information system.

There are over 2500 companies involved in the case nationwide, covering multiple industries such as securities investment, medical insurance, and technology education. At present, the case is still under further investigation.
This case is the first nationwide crackdown on the illegal use of Trojan horses to control computer information systems in enterprise marketing accounts. According to monitoring, after the closure of the case, the number and success rate of trojans deployed by such black and gray production gangs have significantly decreased, eliminating the network and data security risks faced by enterprises.
Next, the Hangzhou Public Security Bureau will guide enterprises in Hangzhou to carry out Trojan horse cleaning and investigation, timely eliminate risks and hidden dangers related to enterprises, and build a strong firewall for enterprise data security. And we will rely on the city wide network security notification mechanism to carry out risk warning and notification, helping enterprises comprehensively enhance their awareness of network security protection and effective anti infringement capabilities.
Police reminder
1. Don't easily open files sent by strangers, pay special attention to files in. exe/. zip/. rar/. bat format.





