How should we prevent it? Undercover overseas forces!, What are the means of infiltration | United States | Infiltration
Not long ago, CIA Director Burns said at a security forum that progress has been made in rebuilding the US intelligence network in China.
We responded with action within less than a month of his wild words.
On August 11th, the Department of National Security released a recently uncovered CIA spy case. There are several details worth noting in this case:
This spy was originally a staff member of a military industrial group and was sent abroad for study by the public;
During his time abroad, he was targeted by the CIA in the United States. After establishing a close relationship with him, the CIA revealed his identity and demanded that he become a spy, promising to pay a huge amount of compensation and handle immigration for his entire family to the United States;
This person agrees to become a spy and receive assessment and training from the US side;
After completing his studies and returning to his home country, this spy continued to provide intelligence to the United States.
The CIA mentioned in this case belongs to what we often refer to as foreign forces.
Who are the current foreign forces, what are the infiltration methods, and how should we prevent them? Tan Zhu found relevant professionals and they provided some clues.
As a typical representative of foreign forces, the CIA has been carrying out operations to infiltrate China.
Especially in the past two years, the CIA has established two specialized centers, the China Task Center and the Cross border and Technology Task Center.
The China Mission Center is the only mission center established by the CIA for a single country. The Cross border and Technology Task Center is responsible for helping American spies improve their espionage technology. The CIA attaches great importance to the application of artificial intelligence technology in cyberspace, and the Chief Technology Officer appointed by the CIA subsequently came from Silicon Valley.

From this, we can see that the United States has a digital trend in infiltrating us. This can also be verified in another department. The US Department of Defense has established an office called the Office of Influence and Cognitive Management. In publicly disclosed materials, it can be found that this institution will influence strategic decisions of other countries through digital analysis results.
This gives us an inspiration that the connotation and extension of overseas forces have already undergone changes.
Tan Zhu found Li Wei, a researcher at the China Institute of Modern International Relations, an authoritative research institution for national security in China.
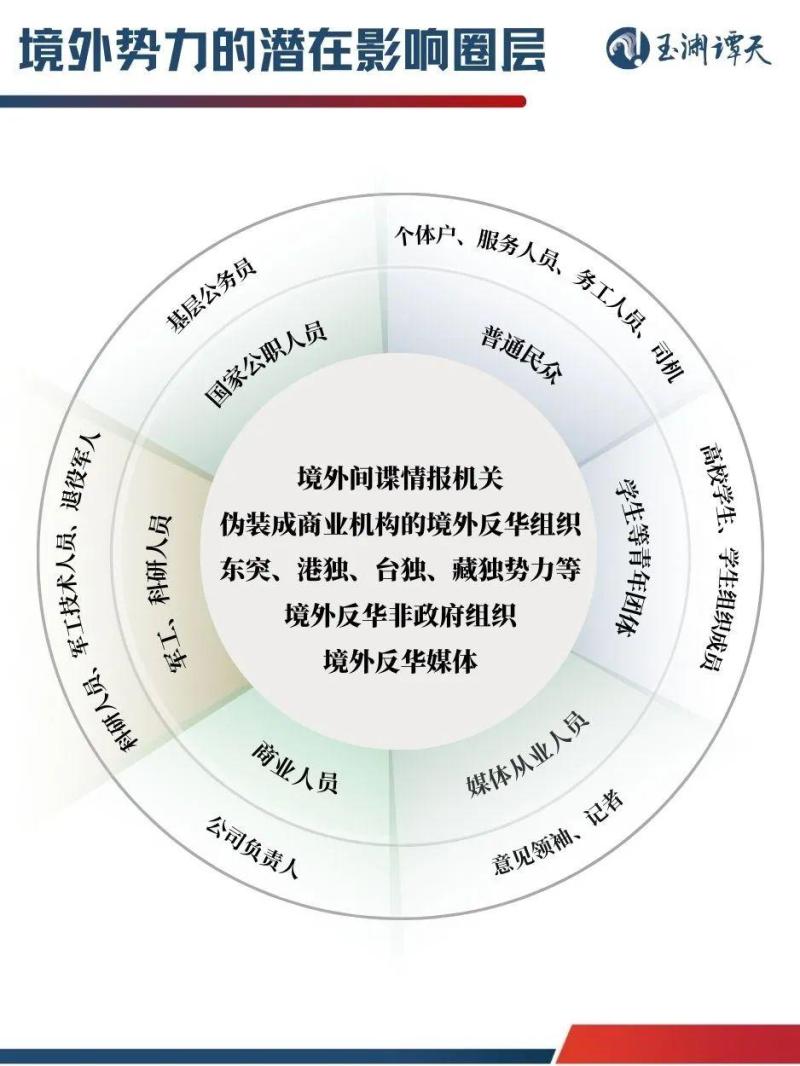
Tan Zhu collected typical cases of foreign forces endangering national security recently announced by national security agencies and created the following image.
Foreign forces can influence people around us because the activity space of ordinary people has been greatly extended through the internet and social media, and foreign forces are very good at burying lines in social media space.
Some of the things that have emerged today may be seeds planted a few years ago.
In a typical case recently made public by national security agencies, there is one related to social media:
Since 2020, some social media accounts have attracted numerous fans under the guise of introducing daily life abroad. Afterwards, these accounts began to carry private goods and frequently spread rumors and slander, publishing content that smeared the image of our country, and even inciting others to violently overthrow the regime.
In social media, these manipulative methods have gone beyond the traditional centralized "peaceful evolution" path and presented the characteristics of multi-point flowering, rapid iteration, and full platform linkage, subtly influencing our cognition through information manipulation.
Rand's research clearly states that certain goals that were previously only achievable by military forces can now be achieved using tools in cyberspace.
Li Wei mentioned that no matter what kind of skin is worn, the entire infiltration activity of the United States and the West into China has a very important characteristic, which is to be consistent with the overall strategy of relevant countries towards China. Where the national strategy of these countries points, their intelligence agencies will adjust their focus accordingly.
This adjustment also corresponds to the competition for cognition.
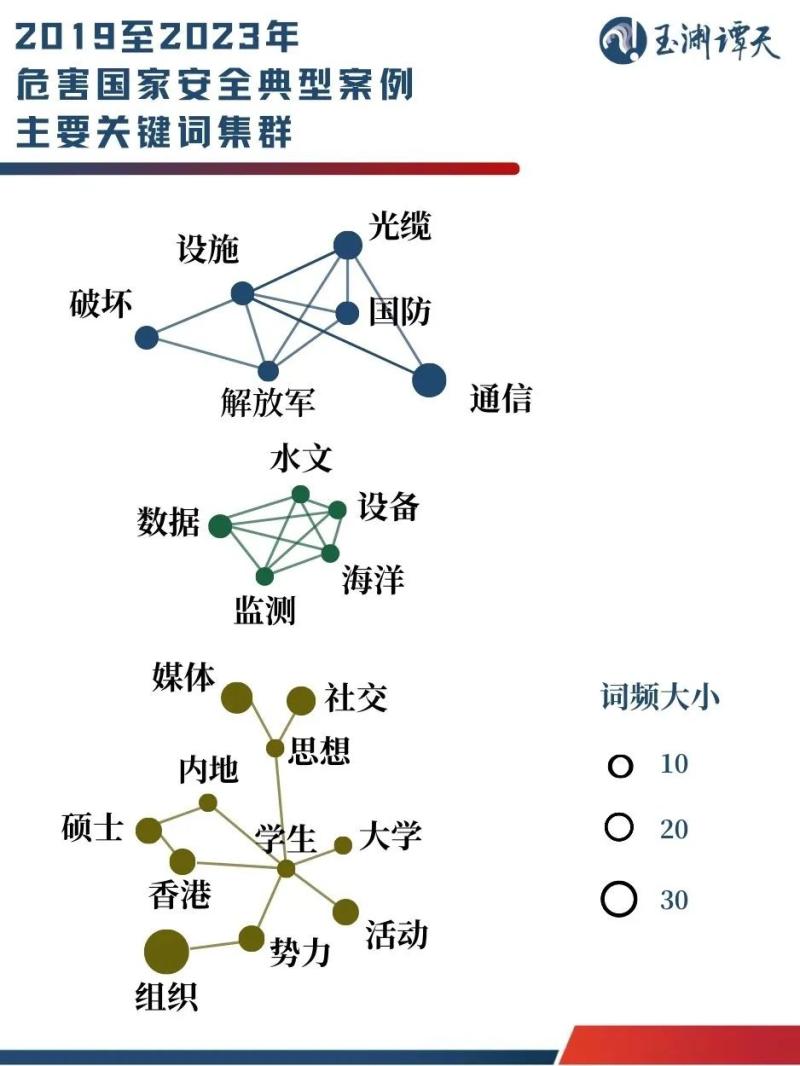
Tan Zhu has sorted out typical cases of endangering national security from 2019 to present, and based on the co-occurrence relationship of keywords, some clustered topic areas can be identified.
Let's start with the military issue in the first cluster in the figure. Regarding military issues, foreign spy intelligence agencies are eyeing our experts in the development of important weapons and equipment, collecting information on our development of cutting-edge weapons. They also bribed ordinary people to observe our military port and instructed them to collect information about warships.
In addition to this kind of "hard confrontation", intelligence gathering is also shifting towards less noticeable directions. Taking the second cluster in the picture as an example, the ocean data involved is also related to the collection of military intelligence.
A group of suspicious foreign personnel once approached an ordinary aquaculture individual in Dalian under the pretext of "free installation of seawater quality monitoring equipment". They nominally help farmers monitor water quality for free, but in reality, these people use this pretext to simultaneously monitor important sensitive data such as tides and currents in non open waters. These data will provide navigation for foreign submarines to secretly infiltrate the vicinity of China's territorial waters.
In addition to these traditional physical challenges, there is also competition in the field of cognition. There are two main techniques for it, one is precise coordination and consistency among multiple departments, and the other is carefully designed for different issues.
We conducted a big data analysis on topics related to our military in the past three months, using the People's Liberation Army of China as the keyword and limiting the search scope to overseas, and obtained nearly 20000 pieces of data. It can be observed that in high-frequency topics, the ratio of the number of topics on which the United States and the West construct China's military threat to the number of topics on China's military assistance is 8:1.
Among them, in addition to anti China media such as Voice of America and Radio Free Asia under the United States International Media Agency, the tentacles that hype up China's military threats and even fabricate rumors about our military have extended outward, including various US defense and intelligence departments.
The goal of this coordination and consistency is very clear, which is to distort China's image and convey this image to two types of people:
One type is countries other than China and the United States, describing China as they are afraid and creating external conflicts.
Everyone should still remember this year's Shangri La Dialogue, where Tan Zhu saw the US Defense Minister shaking hands with the Chinese Defense Minister on the spot, pretending to want to communicate with China. But when he turned around, he said at the meeting that China is creating a military threat to Asian countries and has allowed anti China media to cooperate and hype up.
The second type is the Chinese themselves, who create internal conflicts by constructing images that differ from the Chinese people's perceptions.
In fact, this cognitive competition is not only present in the military field. From the third cluster in the graph, it can be seen that it is also quite cohesive in the social field.

Related professionals and Tan Zhu mentioned a common method used by overseas anti China media: designing different reports for Chinese and English versions, and customizing cognitive guidance. There are also some social media accounts that intersperse a misleading push among the ten neutral ones.
Everyone's cognition is affected in this process. Zhao Hui, Associate Professor of the School of National Security at People's Public Security University of China, pointed out that according to his observation and research, in recent years, overseas anti China media and foreign spies have paid more attention to infiltration and destruction of the social sphere. They use our social contradictions, hot issues, and major events to provoke social conflicts and create group divisions.
It can be seen that multiple agencies, including foreign spy intelligence agencies and anti China media, are collaborating in various military and social fields to launch a "heart attack" war against China.
Besides the above chart, there is another topic that has also become the focus of cognitive competition in the past two years, which is economics. Regarding this issue, the coordinated cognitive guidance methods of the United States and the West have also been exposed.
Prior to the visit of the US Treasury Secretary to China this year, Mr. Tan released a data video focusing on "insiders" in the United States. The only issue that continues to be hyped up by "insiders" in the United States is economic issues, which appear almost every month, most of which are related to sanctions in the chip and technology sectors.
Some of these "insiders" have revealed their units, among which five are densely populated - Congress, Department of Defense, White House, Federal Bureau of Investigation, and Department of Justice. The coordination and consistency of the US government in creating a decoupling atmosphere can be seen.
In summary, the infiltration work of the United States and the West towards us has evolved from traditional theft of national secrets and military intelligence to now influencing people's judgment of events from a cognitive level, creating both online and offline worlds, and changing our expectations of things, thereby influencing our decision-making.
Faced with the rampant infiltration of the United States and the West, China has always been wary of it.
American media has revealed that more than a decade ago, the Chinese system dismantled the CIA's espionage activities in China. In response, some US intelligence officials are pessimistic and believe that the CIA's confidential communication system has been compromised.
As the US spy and intelligence agencies and other collaborative agencies shift their tactics and begin to engage in cognitive battles around us through social media, our means of coping must also change accordingly.
However, all changes are inseparable from their roots. To avoid being changed by others, the key is to have clear thoughts and cognitive coordinates.
How did we do it?
In 2021, when the CIA established the China Mission Center, China proposed the Global Development Initiative to the world; In 2022, when the Office of Influence and Cognitive Management was established by the US Department of Defense, China proposed the "Global Security Initiative" to the world.
Balancing development and security is the fundamental coordinate of China.
Without development, we lack the material foundation to maintain national security, and without security, our development achievements are likely to return to zero overnight.
Just like when you care about whether your bicycle brakes are working properly, you actually want to ride faster. We are now going to the bottom to understand and compete for this security issue, in order to better develop.
We have already seen clearly that the areas of cognitive competition between the United States and the West towards China are completely consistent with the key areas that contain our development.
We have crossed 5000 years of history to where we are today, and we cannot be easily distracted by a 5-second video.
On this basis, we also need to establish a new model of extensive participation and joint prevention.
Last month, the newly revised Anti Espionage Law officially came into effect.
Xiong Qiuhong, Dean of the Institute of Litigation Law at China University of Political Science and Law, introduced that an important point of this revision is to establish a support system for anti espionage work. As the competent authority for anti espionage, national security agencies now place greater emphasis on preventing espionage activities, which requires coordination from various relevant departments and support from every citizen.
Everyone has also noticed that this month, the Ministry of National Security has posted articles on social media to further step up the front line. National security agencies are increasingly emphasizing transparency while carrying out covert work.
This indicates that the cognitive competition on social media is indeed imminent.
Faced with the complex information on social media, if we all ask one more question, is that so? Then their lies will go through another test. When everyone is holding a microphone, if we ask one more question, is it true, then their conspiracy has an extra hope of being exposed.

Dealing with US spy intelligence agencies and other collaborative agencies must also be punished in accordance with the law.
Xiong Qiuhong mentioned a detail that the jurisdiction of the newly revised Anti Spy Law is expanding.
The scope of the subject is expanding, and now establishing spy organizations, participating in spy organizations, and actively joining spy organizations and their agents are all considered espionage activities;
The scope of behavior is expanding, especially targeting cyber espionage, such as cyber attacks and the destruction of our critical information infrastructure.
We have reached the most critical moment, to defend national security, we cannot compromise at all, we cannot compromise at all.
Faced with the infiltration of the United States and the West, the toolbox of the Chinese people is abundant. Today, we are still on the right path of development and standing tall in the east of the world.
Chinese people are not easy to deal with, it is not easy to deal with.




